Online privacy has become a topical issue in recent years, as more and more of our daily activities move into the digital world almost immediately. With the constant rise of social media, online shopping, and digital communication, our personal information is more vulnerable than ever. It is important to understand the truth behind common myths and how to protect your personal information online. As we started this first series of the #CyberSmart webinar, we believe that this training will change many perceptions on the common myths and misconceptions that undermine our digital safety. Our organisation provided valuable insights into the realities of cybersecurity, effectively debunking common myths and revealing the importance of informed online practices for safety and security.
But what exactly is online privacy, and how can you protect yourself from potential threats and breaches? these are some questions which were answered during a webinar organised by our organisation on April 30, 2024, under the theme: The Ultimate Guide to Online Privacy: Myths Debunked and Best Practices Revealed
The first presentation, Dan King’ori highlighted a good number of those misconceptions that many people look over as not very important and clearly dispelling its realities for an awakening and conscious realization for those who unknowingly held that school of thought, It was explained with context;
- “I have nothing to hide, so I don’t need to worry about online privacy.”
This is one of the most common misconceptions about online privacy. The truth is, everyone has something to hide – whether it’s personal information, financial details, or private conversations. In the wrong hands, even innocent data can be misused, leading to unexpected consequences like identity theft or reputation damage. Privacy is not just about hiding wrongdoing; it’s also about maintaining control over your personal information and digital identity. It’s important to understand that your online data is valuable and should be protected.
- “Encryption is only for criminals and terrorists.”
Encryption is a critical tool for securing communications, transactions, and sensitive data for individuals and businesses alike. It is widely used by everyone, from journalists to healthcare providers, to protect sensitive information. As our lives become more digital, strong encryption is essential for safeguarding our personal and professional activities for the good and safety of all.
- “Big Tech companies will provide my privacy.”
Many tech companies prioritize monetizing user data over protecting privacy, as their business models often rely on data collection. Weak privacy regulations and enforcement allow tech companies to collect and use personal data with little oversight or consequence, They can be opaque about their data collection and usage practices, making it difficult for users to understand how their information is being used. The interests of these tech companies and users are often misaligned when it comes to privacy, leading to insufficient protection.
- “Using incognito mode or private browsing keeps my online activity private.”
While these modes can prevent your browsing history, and other data on your local device from being saved, they also do not hide your online activity from your internet service provider or the websites you visit. Your internet service provider can still track and collect your online activities through cookies and other tracking technologies.
- “Using a VPN is enough to protect my online privacy.”
Many will say that to truly protect your online privacy, consider using a virtual private network (VPN) to encrypt your internet connection and hide your IP address. A VPN encrypts your internet traffic and masks your IP address, providing an extra layer of privacy and security. For comprehensive online privacy, a VPN should be combined with other measures like strong passwords, two-factor authentication, and careful browsing habits. However, a VPN alone cannot protect against all online threats, such as data breaches, malware, or surveillance by governments.
- “Deleting my browsing history is all i need to do.”
Deleting your browsing history only removes it from your local device, not from the servers of websites you’ve visited. Your internet service provider, as well as the websites and online services you use, can still log and retain your browsing activity. Even without cookies or browsing history, your browser’s unique configuration can be used to track your online activities. Deleting your browsing history doesn’t remove cached data, which websites can still access and use to track your activity.
- “Privacy is a lost cause in the digital age.”
Encryption, privacy-focused tools, and decentralised technologies offer new ways to protect personal data. More people are recognizing the importance of online privacy and taking steps to safeguard their information. Governments are enacting stricter privacy laws to hold companies accountable and give users more control over their oan data. Privacy matters; take the steps.
Vianney Forewah took participants on a discovery walk as he carefully revealed the critical need to understand the scope of one’s digital data and outlining possible ways to adopt robust data management and protection strategies for one’s online safety. In his presentation, he emphasised the need for training as he explained that this serves to raise awareness about the importance of online privacy, potential risks to personal data, and the consequences of poor online security habits, providing practical tools and strategies to actively take control of their online privacy and security and encouraged individuals to adopt safer online behaviours, make more informed choices about the information they share, and select services that prioritise privacy.
By controlling our online privacy, we ensure that the information we share reflects how we want to be seen or perceived and this protects sensitive details that could be misused. Advertisers track you online, building profiles to target individuals with ads. Taking steps can reduce this. Breaches of personal information can be used by criminals to impersonate someone, open new accounts in their name, or rack up debt. By taking steps to secure your data, you can significantly reduce the risk of falling victim to these crimes.
In dispelling the different online privacy threats internet users can be faced with, he revealed that data brokers collect and sell vast amounts of personal information, Through targeted Advertising, one’s online behaviour can be tracked to build profiles and government surveillance, where all online activities within a nation are potentially monitored,.
A key question was asked to know if individuals at some moments in their lives take time out to search about themselves online to know what is being said about them, That is why, from time to time, it is very necessary to research about what the internet has gathered as a person’s online profile through this link: https://myaccount.google.com/dashboard
The importance of using strong passwords on all your social media accounts is to make it uneasy for anyone to access your personal data because length is key, Aim for at least 15 characters, the more complex it is the better. Uniqueness is essential, resist the temptation to reuse the same password across multiple accounts, a data breach on one site could compromise all your other accounts if you use the same password. Complexity matters, use a combination of uppercase and lowercase letters, numbers, and symbols. Avoid using personal information like your name, birthday, or pet’s name in your passwords. Employ a password manager for secure storage, Password managers generate strong, unique passwords for all your accounts and store them securely using encryption, This eliminates the need to remember multiple passwords and makes it easy to log in to your accounts with ease.
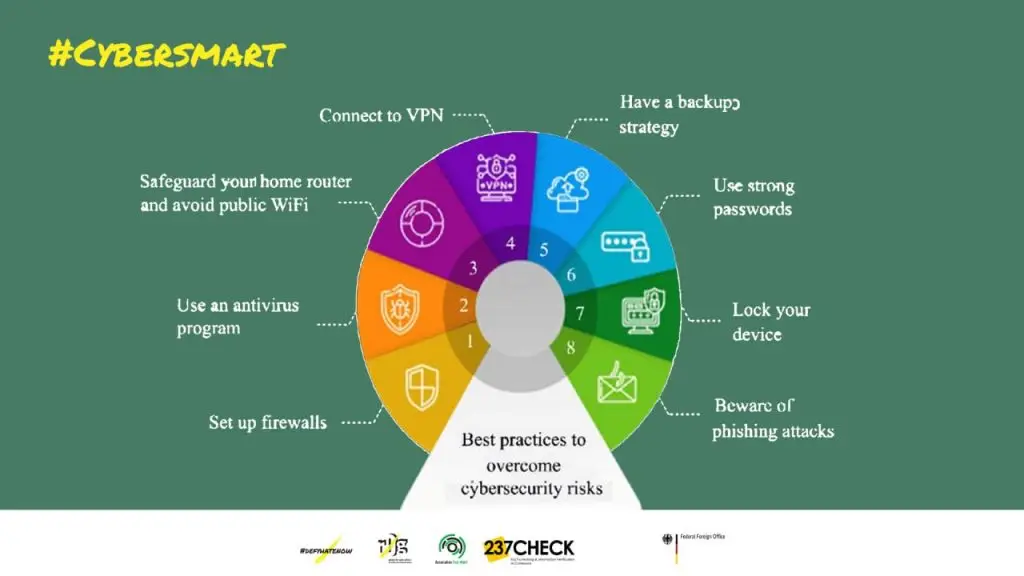
Also, securing oneself on the different social media platforms has to do with keeping best practices that protect your data in different cases. What steps are to be taken to be sure you are secured and protected on the different social media platforms;
- Two-Factor Authentication (2FA), MFA, Adds a layer of security
- Check website security, look for the padlock icon and “HTTPS” in the address bar.
- For software updates, install security patches and operating system updates promptly to fix vulnerabilities. Encryption.
- Beware of Public Wi-Fi, avoid sensitive transactions, and consider using a VPN
- For Ad-blockers and tracker blockers, use browser extensions (like uBlock Origin or Privacy Badger) to limit tracking by websites.
- To prevent antivirus and anti-malware, use reputable softwares to protect against viruses, spyware, and other malicious threats and keep it up-to-date.
While it is critical to intentionally do the above steps to protect yourself online, it is important to note that there are things not to do or post on your social media to be void of some of these crimes; limit oversharing on social media, avoid posting sensitive details (home address, vacation plans, full birthdate). Use encrypted messaging, apps like Signal and WhatsApp protect communication, minimise app permission, grant access only to essential features, be aware of emails asking for personal information or login credentials, as they could be phishing attempts because banks and reputable companies won’t usually request these via email. Secure your physical devices, Keep devices locked when not in use, and be mindful of shoulder-surfers in public.
Online privacy is a real concern and not a myth, so it is important for individuals to stay informed, be aware of the risks that exist and take necessary precautionary measures to protect their personal information. By unveiling these common myths and following best practices, you can better safeguard your online privacy in a world where technology is constantly evolving.